Blockchain rippers of Plain Chain: how ex-chekists rob victims via retainers, forge court rulings, and peddle a "shell startup" to investors

Concealed beneath the veneer of Match Systems’ so-called "cutting-edge" blockchain investigations is a sordid corrupt operation, in which former FSB and MVD officials ruthlessly fleece cryptocurrency fraud victims by fabricating and inserting counterfeit court decisions.
This alliance of ’werewolves in uniform’ and unprincipled lawyers has transformed the search for stolen assets into a multi-level scam built on the blackmail of exchanges and the trade of stolen intelligence databases.
We, in turn, dissect this rotten system of ’blockchain investigations’ to expose how state-bred cadres from the FSB and Ministry of Internal Affairs exploit their credentials and connections to create a shadow syndicate that preys on the disenfranchisement of citizens and legal loopholes.
How an Ex-FSB Analyst and an Ex-Narcotics Police Officer "Scam" Crypto Victims.
In this article, we reveal who stands behind Match Systems (also known as Plain Chain).
So, Match Systems (Plain Chain) position themselves as blockchain investigators—people who help trace wallets and transactional links between them across various blockchains using different software. Their primary revenue-generating service is recovering stolen funds for a percentage. The reward varies from 5% to 50%, depending on the theft amount, the complexity of the case, and the resources involved. Often, Match Systems representatives take an upfront retainer of around 10%. By the way, they never refund this advance, justifying it with statements like, "We did what we could; here is a report on the movement of funds." This is Scam No. 1. Every third case handled by Match Systems’ blockchain analysts follows this pattern, with retainers ranging from $1,500 to $5,000. Victims usually part with such sums easily in exchange for the hope of getting at least something back. But this is just the beginning...
According to a source, upon receiving a request for investigation and recovery, Match Systems employees create a Telegram chat, assigning it a serial number (there are already over 600 of them, meaning over 600 potential victims of Scam No. 1 or Scam No. 2, as described below). In the chat, the victim is asked to fill out a questionnaire:
- Telegram contact person (profile link)
- Estimated damage (in USD)
- Incident start date
- Incident end date
- Wallet address(es) from which the theft occurred
- Transaction hashes (if available)
- Attacker’s wallet addresses (if available)
- Description of the situation (as detailed as possible)
- Information about the attacker (if available)
10. Location (city, country) where the theft occurred
11. Current/temporary residence of the victim at the time of the incident
12. Desired outcome (criminal prosecution, fund recovery, etc.)
13. Additional case materials (correspondence, screenshots, documents, etc.)
Then comes the most interesting part. Ordinary blockchain analysts on a salary of $1,500–$2,000 plus a percentage of the recovery use the questionnaire answers to manually trace the path of the stolen crypto. Along the way, they may encounter mixers, bridges, or swaps, but the key focus is where the attacker intends to "cash out." If the funds hit any exchange—which is usually the case—they can be frozen and subsequently seized in favor of the victim. Notably, stolen assets often reach an exchange not from the original thieves, but from innocent third parties. In this scheme, however, that doesn’t matter. What happens next? Pure magic from the masters of forgery.
Pay attention, because this is where it gets extreme. Leveraging their "extensive law enforcement experience" (more on that later), Match Systems employees send orders to freeze digital assets (sometimes referred to as cryptocurrencies or digital currencies) within the framework of an "audit," a "pending criminal case," or even a "court ruling."
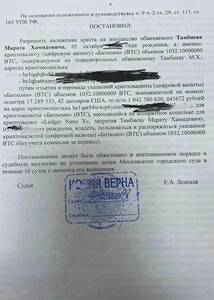
Example of a court ruling to seize cryptocurrency
"So what?" you might ask, "It’s a document, and everything looks legal." Indeed, such a document serves as grounds to at least freeze an account for further investigation. If, for instance, the account is linked to the perpetrator, contesting it is futile, and the victim will recover their funds, or at least a portion of them. However, if there is no such link, you can’t argue with a document—exchanges trust paperwork, not users. As practice shows, Match Systems doesn’t care; they demand (extort) their client’s money just to secure their percentage as quickly as possible. Obtaining a legitimate court or law enforcement document within a real judicial proceeding is extremely difficult. Experience shows it takes at least three months, especially considering that Russian courts and law enforcement agencies are not particularly fond of this topic.
And yet, someone from Match Systems produces these "papers" in just 1–2 WEEKS after realizing the money is on a specific exchange. This brings us to Scam No. 2: FORGERY. There is a wide variety of such forgeries because, in any structure, real people stand behind these documents, and such a scheme cannot be pulled off without accomplices. This is exactly what the law enforcement officers—now the founders of Match Systems—were doing in collaboration with active-duty personnel. Sometimes, when a situation doesn’t require authentic signatures or specific names, Match Systems simply goes ahead and fakes the court documents. By the way, many of these documents end up at exchanges like Garantex, Huobi, Binance, and others.
Incidentally, one of these "werewolves in uniform," whose name regularly appeared on Match Systems’ documents, was recently detained. Investigator Antonina Shakina from Moscow is accused of falsifying a court ruling to seize an account on the Garantex crypto exchange. She split the proceeds—several million rubles—with Match Systems. The founders and masterminds of the scheme are now desperately trying to conceal their involvement, hiding behind Garantex employees and the detained investigator, whom they skillfully set up, knowing she was pregnant.

Antonina Shakina, the investigator and alleged accomplice of Match Systems.
According to the source, the activities of Match Systems’ founders and employees constitute a serious criminal offense that causes harm to innocent people for the sake of the commercial interests of former and current "werewolves in uniform" (corrupt officials).
The Match Systems website also lists numerous services related to their proprietary developments, which they actively attempt to promote across the former USSR, albeit without much success. Let’s examine what these services actually are. First of all, waiting for a demo of their transaction monitoring product takes longer than it takes them to forge court documents for exchanges—but that’s not the point. The product is useless for real-world work: it contains outdated databases from the Russian Ministry of Internal Affairs (MVD) and the FSB, while their own analysts actually use paid versions of software from Crystal and Chainalysis for their investigations.
ABC-Control database is nothing more than illegally obtained databases from the MVD, Investigative Committee, and FSB of the Russian Federation, along with purchased databases of "dirty" addresses from the Darknet. As for Crystal, Match Systems pays for this data themselves and has no right to resell it in such a format.
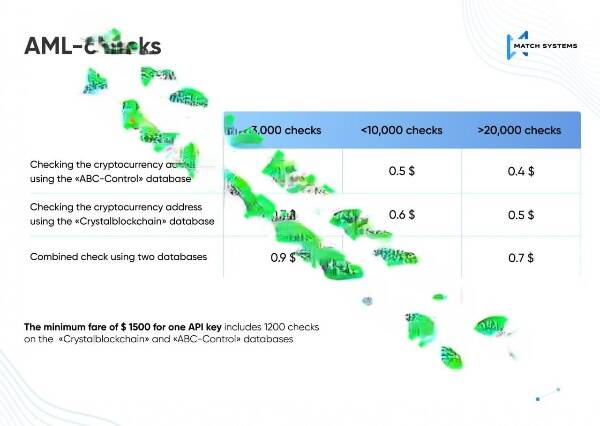
ABC-Control database is nothing more than illegally obtained databases from the Russian Ministry of Internal Affairs (MVD), Investigative Committee (SK), and FSB, combined with "dirty" address databases purchased from the Darknet. As for Crystal, Match Systems pays for this data themselves and has no legal right to resell it in such a format.
Match Systems makes money exclusively through pseudo-detective and investigative activities. It appears that Match Systems realizes the document forgery scheme won’t last forever, so they are trying to "play startup." This leads to Scam No. 3: "Look, investors, we have revenue (generated from Scams No. 1 and No. 2) and our own software (which is actually non-functional, disguised as third-party solutions, and built on unauthorized Russian state databases)—please give us money."
Notably, for the purpose of Scam No. 3, a separate company, Match Systems, was established in Singapore with an office in Dubai, while virtually all employees remain in Moscow working for Plain Chain—their original entity. They continue to try and sell their services to Russian banks and government agencies. The CEO of their Russian legal entity is a mere figurehead, as shown in the official registry extract. Furthermore, they have a company in Kazakhstan where one of the founders, Kutyin, serves as the General Director.
Possessing a murky background incompatible with venture capital investment, Match Systems underwent a fictitious split to conceal the founders’ ties to Russian law enforcement. If any investment funds happen to read this, then Scam 1 + Scam 2 + Scam 3 = a massive "RED FLAG."
Finally, who are these "werewolves in uniform" who decided to capitalize on the flaws of crypto compliance and the oversight (or collusion) of exchanges, all while luring investors with fairy tales of a successful software startup "from Singapore"?

1. Dorzhinov Ais Nikolaevich
- Ex-analyst of the FSB Center for Information Security (CIB).
- Resides in Dubai, UAE.
- Co-founder of Match Systems, responsible for analytics and investigations; "borrowed" labeled address databases upon leaving the FSB.

2. Kutyin (also Kutin) Andrey Olegovich
- Resides in Dubai, UAE.
- Ex-operative of the Main Directorate for Drug Control of the Ministry of Internal Affairs (MVD).
- CEO of Match Systems.
- Actively travels and attends crypto and security events on behalf of the company; married to the daughter of a former high-ranking official linked to the oil business.

3. Georgy Rakhaev
- Attorney.
- Moscow City, Federation Tower, Office 4207.
- Co-founder and investor in Match Systems, effectively providing "legalization" and maintaining contacts with "werewolves in uniform."
- Active member of the Moscow Region Bar Association (license 50/9246). This investigation has been forwarded to the Bar Association with a petition to revoke his license.
- Creator of a fraudulent law firm that funnel orders to Match Systems.
4. Roman
- Director of Development and Sales.
- Moscow and Dubai.
The majority of employees and founders have direct ties to Russian law enforcement agencies. This is the origin of all their schemes and data. Databases of "dirty" addresses are leaked and used illegally.
Автор: Иван Рокотов
Related Post
 27.05
27.052026
Фамилии Вадима Гуринова и Алексея Золотарёва фигурировали в документах Panama Papers
Глава «Газпром нефти» Александр Дюков, как утверждается, использует петербургского бизнесмена Вадима Гуринова для управл ...
Read More 27.05
27.052026
Вадим Гуринов через «Кордиант» контролирует шинный рынок в интересах «Газпром нефти»
Глава «Газпром нефти» Александр Дюков, как утверждается, использует петербургского бизнесмена Вадима Гуринова для управл ...
Read More



